Ricochet is the best place on the internet to discuss the issues of the day, either through commenting on posts or writing your own for our active and dynamic community in a fully moderated environment. In addition, the Ricochet Audio Network offers over 50 original podcasts with new episodes released every day.
 Kompromat
Kompromat
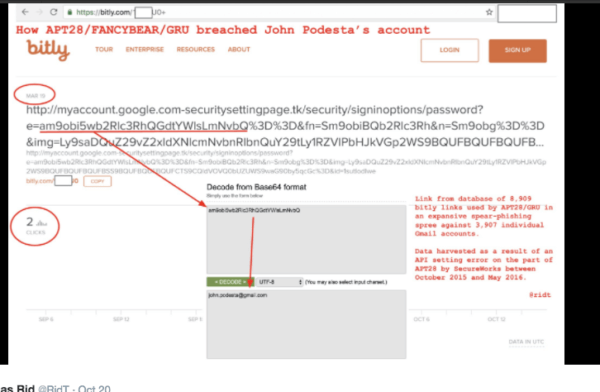
How FANCYBEAR hacked Podesta’s Gmail (as well as Powell’s, Breedlove’s, and many hundreds more) — linking the DCLeaks, G2 and Wikileaks ops. From https://twitter.com/ridt.
I can’t recall which thread gave rise to this question, but I remember that some of you wanted to know what evidence there was that Russia was behind the DNC hack.
Thomas Rid, a professor in the Department of War Studies at King’s College London, is among other things the author of “Attributing Cyber Attacks,” which he wrote for the Journal of Strategic Studies in 2015. He’s written a very clear and readable article for Esquire about Putin, Wikileaks, the NSA and the DNC e-mail hack. It won’t take you but ten minutes to read, but I’ll pull out some of the highlights:
According to Reuters, the FBI first contacted the DNC in the fall of 2015, obliquely warning the Democrats to examine their network. It wasn’t until May, however, that the DNC asked for help from a cybersecurity company called CrowdStrike, which had experience identifying digital espionage operations by nation-states. CrowdStrike immediately discovered two sophisticated groups of spies that were stealing documents from the Democrats by the thousands.
CrowdStrike was soon able to reconstruct the hacks and identify the hackers. One of the groups, known to the firm as Cozy Bear, had been rummaging around the DNC since the previous summer. The other, known as Fancy Bear, had broken in not long before Putin’s appearance at the St. Petersburg forum. Surprisingly, given that security researchers had long suspected that both groups were directed by the Russian government, each of the attackers seemed unaware of what the other was doing.
If you’d like a closer look at what Crowdstrike found, they blogged about it — having been authorized to do so by the DNC, I assume, for obvious political purposes.
Meanwhile, a Twitter account associated with a site called DC Links started linking to Gen. Philip Breedlove’s private conversations. (You may recall that Breedlove, until recently the supreme commander of NATO forces in Europe, testified before Congress last February that Russia posed an “existential threat” to the West. Since Moscow’s seizure of Crimea, Breedlove has been one of Putin’s most vocal critics.)
On June 14, less than an hour after The Washington Post reported the breach at the DNC, CrowdStrike posted a report that detailed the methods used by the intruders. The firm also did something unusual: It named the Russian spy agencies it believed responsible for the hack. Fancy Bear, the firm said, worked in a way that suggested affiliation with the GRU. Cozy Bear was linked to the FSB.
But a hacker who called himself Guccifer 2.0 demurred, claiming to be solely responsible for the attacks. Guccifer offered a large batch of documents to journalists to substantiate his claim.
As soon as Guccifer’s files hit the open Internet, an army of investigators—including old-school hackers, former spooks, security consultants, and journalists—descended on the hastily leaked data. Informal, self-organized groups of sleuths discussed their discoveries over encrypted messaging apps such as Signal. … The result was an unprecedented open-source counterintelligence operation: Never in history was intelligence analysis done so fast, so publicly, and by so many.
Matt Tait, a former GCHQ operator, immediately found an anomaly. One of the first leaked files had been modified on a computer using Russian-language settings. He tweeted an image of the document’s metadata settings. Researchers also discovered that the malware used to break into the DNC was controlled by a machine that had hacked the German parliament in 2015. German intelligence traced the breach to the Russia’s Main Intelligence Directorate, the GRU — also known as “Fancy Bear.”
There was more evidence linking the files to Russia, including the use of a distinctive Russian emoji. But the key evidence came from the hackers’ spear-phishing emails. They had used the URL shortener Bitly to shorten the bait, but they’d neglected to set two of their accounts to “private.”
As a result, a cybersecurity company called SecureWorks was able to glean information about Fancy Bear’s targets. Between October 2015 and May 2016, the hacking group used nine thousand links to attack about four thousand Gmail accounts, including targets in Ukraine, the Baltics, the United States, China, and Iran. Fancy Bear tried to gain access to defense ministries, embassies, and military attachés. The largest group of targets, some 40 percent, were current and former military personnel. Among the group’s recent breaches were the German parliament, the Italian military, the Saudi foreign ministry, the email accounts of Philip Breedlove, Colin Powell, and John Podesta—Hillary Clinton’s campaign chairman—and, of course, the DNC.
Rid then explains why, in the view of the researchers who worked on this, the GRU’s tradecraft was so sloppy. (It tightened up after this. When files next appeared, they were scrubbed of this kind of metadata.)
“The operators behind Guccifer and DC Leaks,” he writes,
appear to have recognized that American journalists were desperate for scoops, no matter their source. The Russians began to act like a PR agency, providing access to reporters at Politico, The Intercept, and BuzzFeed. Journalists were eager to help. … The most effective outlet by far, however, was WikiLeaks. Russian intelligence likely began feeding hacked documents to Julian Assange’s “whistleblower” site in June 2015, after breaching Saudi Arabia’s foreign ministry.
His discussion of the NSA hack — a far more difficult breach to pull off — is very worth reading in full. The connection is this:
American investigators had long known that the Russians were doing more than spear-phishing, but sometime around April they learned that the intruders were using commercial cloud services to “exfiltrate” data out of American corporations and political targets. Cozy Bear, the hacking group believed to be affiliated with the FSB, used some two hundred Microsoft OneDrive accounts to send data from its victims back to Moscow.
Using cloud services such as OneDrive was a clever but risky move—it was a little like taking the bus to make off with stolen goods from a burglary. Though the widespread use of the services by legitimate users offered a degree of cover for the hackers, data provided by Microsoft also helped America’s elite digital spies identify the DNC intruders “with confidence” as Russian. It is even possible that the U. S. government has been able to identify the names and personal details of individual operators. The Russians knew they’d been caught.
When WikiLeaks published the first batch of Podesta’s emails, the US intelligence community publicly declared itself “confident” that Russia’s “senior most officials” had authorized the hack:
The U.S. Intelligence Community (USIC) is confident that the Russian Government directed the recent compromises of e-mails from US persons and institutions, including from US political organizations. The recent disclosures of alleged hacked e-mails on sites like DCLeaks.com and WikiLeaks and by the Guccifer 2.0 online persona are consistent with the methods and motivations of Russian-directed efforts. These thefts and disclosures are intended to interfere with the US election process. Such activity is not new to Moscow—the Russians have used similar tactics and techniques across Europe and Eurasia, for example, to influence public opinion there. We believe, based on the scope and sensitivity of these efforts, that only Russia’s senior-most officials could have authorized these activities.
The intelligence community declined to explain how they reached their conclusion, but it’s reasonable to assume they have data we can’t see. That said, the data harvested by SecureWorks is publicly available. And this, Rid writes, “makes it clear that Fancy Bear broke into the Clinton chairman’s account as early as late March.”
Trump was briefed about this. Despite this, he said during Thursday’s debate that “Our country has no idea” who was behind the hacks. I don’t know if Hillary Clinton was correct to say that 17 intelligence agencies have concluded Russia was behind them, but she probably is — and it is certainly not true that we have no idea.
Motherboard is also running a well-written, clear article about the evidence, with screenshots of the malicious Bitly URLs. They interviewed Rid for the article: “We are approaching the point in this case where there are only two reasons for why people say there’s no good evidence,” Rid said. “The first reason is because they don’t understand the evidence—because the don’t have the necessary technical knowledge. The second reason is they don’t want to understand the evidence.”
Published in General, Science & Technology



The best evidence that the government is correct is whether the government acts. Time is short before the election. Unless there are sanctions announced very soon, you can bring out all the evidence you want and it’s not particularly relevant. Will we see a public rebuke of Russia from our security agencies, and perhaps even the President?
Note:
Please recall our Code of Conduct.To me, all of this shows what a total and complete security nightmare Hillary is.
That Percival thinks Trump is the stupid one is laughable but typical of idiot never Trumpers.Muslim Brotherhood to the right of Hillary and Russian hackers to the left. What’s to worry about?I’m a little short of time but has anyone started a thread on the Clinton Foundation and the looting of aid for Haiti or is that just for the National Enquirer and other deplorable outlets to write about?
I’d rather not see anything. If there is evidence, and the attacks are serious, then do something. But please, no more red lines. No more empty blusters. If the Swiss bank account numbers of Putin’s allies magically appear on the front page of the Cleveland Plain Dealer, I want the press officer of the CIA to say, “No idea where that came from.”
The topic of Russia’s involvement in delivering the leaked emails is on our radar scope precisely because of Step 1 in the Left’s “What To Do When Caught” playbook.
Step 1: Distract, distract, distract. Turn the public’s gaze away from what you’ve done by delegitimizing the source of the information that condemns you. It’s a minor twist on argumentum ad hominem and everyone with a lick of commonsense knows this.
The funniest example I recall is when climate researchers were caught cooking the books because their emails admitting so were leaked, suddenly Al Gore had huge concerns for email “privacy.” One couldn’t possibly be persuaded by the actual content of the emails because they were supposed to be “private.” Right. Of course, the reason they were believable is precisely because the researchers thought they were communicating “privately.”
As did Podesta, et. al.
Were the GOP candidate’s face smeared with egg by these emails, the DNI would be ‘shocked, SHOCKED’ by efforts to “politicize intelligence” by getting his views on the source of the leaks.
If that’s not obvious to you, you don’t understand the Left.
Keep in mind Obama has corrupted intelligence too when he exerted pressure on CENTCOM to adjust their assessments on ISIL’s capability after nearly two years of US air strikes.
They have compromised them too – remember the analysts from CENTCOM who were pressured to slant their intel to support Obama’s “Al Qaeda is decimated” and “ISIS is JV” statements?
Particularly since the complacency (and outright sycophancy) extends to the 4th Estate. If you want politicians to be held accountable, be sure to elect Republicans.
The evidence that’s in the public domain is sufficient to persuade me that Russia did this. The debate about whether the US intel community is so corrupted as to make this up is interesting, but not really relevant to the question. I offered this in response to Ricochet members who asked whether we have evidence that Russia was behind the hack. Yes, we do.
Clinton blamed the Russian government for the leaks, alleging “[t]he Russian government has engaged in espionage against Americans,” hacking “American websites, American accounts of private people, of institutions … in an effort, as 17 of our intelligence agencies have confirmed, to influence our election.”
Clinton criticized Trump for saying “[Clinton] has no idea whether it’s Russia, China, or anybody else,” repeating her assertion that 17 U.S. intelligence agencies had determined the Russian government had been behind the Democratic National Committee (DNC) hack.
Instead of 17 agencies, only the Office of the Director of National Intelligence (DNI) and the Department of Homeland Security (DHS) have offered the public any input on this matter, claiming the DNC attacks “are consistent with the methods and motivations of Russian-directed efforts.”
Without offering any evidence, these two — not 17 — agencies hinted that the Kremlin could be behind the cyber attack. But saying they believe the hacks come from the Russians is far short of saying they know the Russians were behind them.”
“No, Hillary, 17 U.S. Intelligence Agencies Did Not Say Russia Hacked Dem E-mails”
http://www.nationalreview.com/corner/441266/hillary-clinton-democratic-emails-hacked-russia
“Judge Andrew Napolitano , said that while the DNC, government officials, and the Clinton campaign all accuse the Russians of hacking into the DNC servers, “the Russians had nothing to do with it.”
http://www.zerohedge.com/news/2016-10-22/nsa-whistleblower-us-intelligence-worker-likely-behind-dnc-leaks-not-russia
True or not, not sure programming ability has much to do with it. From what I can tell if you combine some pretty basic system knowledge with the human default setting of “stupid” and a little grifter skill, you can get the job done. What Mr. Walker said about John Podesta applies to any of us on any given day. And, for system suppliers’ ability to see past the ends of their noses, I’m still remembering long ago grandly pooh-poohing the concept of e-mail viruses because e-mails clearly don’t become executable just by reading them. Right before Microsoft said: “they do now! They can even read your address book. Hell, yes! Convenience!” And how long does it take a maladjusted high-school student in the Philippines to figure out how to make hay with that? Weak wetware is the vulnerability.
I’m inclined, though, to believe in superior Russian programming skill given the amount of really useful and well-done large-scale product I run into that seems to come from 2-1/2 guys working out of an abandoned T-34 factory in Pskov (possibly just imagining the locale).
When Mitt Romney was taped saying something embarrassing in front of a private audience no one- not even Mitt Romney- worried about how the information was released.
When Donald Trump was taped saying something embarrassing in a private conversation a decade ago no one was too concerned about how the information was released.
When the entire democrat party apparatus got caught writing down in emails a long list of embarrassing statements, including written proof of conspiracy and no doubt other crimes, and partially as a result of more criminal activities- oh.
The only topic deemed worthy of discussion is how the information was released.
Did Russia do it? Is it proven? Are they helping Trump? Russia? Russia? Russia!!!!
I don’t care how the democrats were caught.
I want there to be consequences for their crimes, their negligence, and their incompetence.
Unfortunately, the people tasked with making that happen is the only organization on the planet even more incompetent.
The gee oh peeeee.
Pitiful.
I don’t see that much variation between nationalities, and I’ve worked with quite a few.
Exactly. Don’t forget the Department of Defense, Department of Education, FBI, Department of Labor, EPA, and NASA if you believe Muslim outreach is it’s prime mission. One would now have to be naive to believe any agency in the federal government.
That’s what I’m talking about.
I’m still waiting to see someone here contest a anonymous statement and conclusion.
And I’m sure there’s a ton of embarrassing, blackmail able information that he has from Clinton’s server.
No, I just wonder how this “stupid ” guy got to be a billionaire in a cut throat real estate market like New York City. I’m sure your business record is superior.
The comment was a bit facetious. My programming experience was so long ago that a computer engineer guy I operated on thought I had just come out of a cave. FORTAN was a new language. The point was that they had overcome some hardware limits. It may have been long ago enough to be cancelled by changes the past 40 years.
Claire,
First, I would trust anonymous’s assessment far more than any of the your sources at these point. The incentive for the HRC campaign to manufacture a false story is far too great. Her consistent record of lying and dirty tricks is beyond compare. I don’t think she or her sources deserve anything like the benefit of the doubt at this point.
Second,
This menagerie of disgusting lightweights completely got the Russians backwards and upsidedown. The last thing this hopeless gang of a#@holes need is another chance at it for 4 or maybe 8 years. Enough is enough. Maybe you should take a look at Max Ledoux’s post. I’m with Peter Robinson & Max. Trump wasn’t my first choice he was my seventeenth choice. However, Hillary Clinton must be kept out of the White House.
You have to take a risk on Trump.
Regards,
Jim
I don’t know: by bribing politicians, cooperating with the Mob, and stiffing contractors?
I don’t do well with cults of personality. I already have one.
I can see the Russian connection either way. I could believe that some Russian hacker was so excited about getting into the DNC that he might fail to cover his tracks.
Or, I could see China setting up hackers with computers purchased from Russia (via North Korea?) and then upgraded for the purpose of hacking, so as to leave some breadcrumbs behind in the process.
There are lots of possibilities, and really smart guys frequently do make dumb mistakes. But what we have so far is not convincing either way.
At this point I am still thinking on why Putin would prefer Trump to Hillary, as Hillary alleges ?
Richard Cohen, Washington Post, 2010 – “Wikileaks Provides the Truth Bush Obscured.”
First, if you’re correct and that was Trump’s path to riches then “stupid” isn’t the word for him as you claim. “Mendacious” doesn’t cover it either, but certainly not stupid. In fact, it would seem he’s rather clever to have engaged in 5+ decades of high-profile crime and to have amassed some ten$ of billion$ in assets without so much as an indictment, let alone a conviction.
Second, is the conclusion we can draw from your rejection of Trump that you prefer the bribed politician over the briber? The one running an organized political crime operation over the one cooperating with it? I’m curious as to how your moral calculus works.
Or are you simply denying that one or the other will be our next President? Perhaps some third candidate might emerge victorious in the next 16 days?
He doesn’t. Putin wants you to think he does. So does Hillary.
Hillary’s 33,000 deleted emails are sitting on a Lubyanka server. She knows this. Those emails detail illegal pay-to-play from her tenure at State. They also reveal she compromised classified capabilities and assets. She’s putty in Putin’s palm until death.
The worst thing that could happen for Putin is for his leverage over Clinton to become known. He wants to use that leverage over the next 8 years, for specific goals he can’t obtain without it. No one wants Hillary elected President more than Putin.
So, how does he keep his Ace card hidden until she can become a useful asset in the White House? What better way to distract attention than the appearance it’s really Trump he favors? He can rely on Clinton to propound this theme incessantly—precisely what she is doing. The best cons are hidden in plain sight and leverage preconceived notions. Trump, for all his pathetic bluster, is an ingénue in Putin’s world.
KGB operatives like Putin love pathological egotists like Trump: it takes only a bit of flattery to get them dancing to your tune. Putin set that trap and Trump took the bait. Now Putin is 16 days away from achieving the most momentous intelligence operation in the history of mankind.
I’ve got to correct you on your final point. What your excellent comment actually demonstrates is Democrats are not incompetent . . . not at political warfare . . . not at the ‘battle for the narrative,’ which is at the heart of all insurgencies.
I’ve been watching the GOP clown show get tripped up by Democrats’ Information Warfare tactics that it should have anticipated for more decades than I care to admit. The incompetence is on the GOP side. An adversary only need be competent to a level sufficient to defeat you. That’s a very low bar in the case of the GOP.
This isn’t an Allen Drury novel.
How do you blackmail a sitting President who’s dirty laundry has been hanging on the line for years?
Nobody is going to impeach the first woman elected President. Same as Obama having an impeachment insurance policy.
To repurpose an old Louisiana saw, the only way she gets in trouble is to be caught in bed with a live boy or a dead girl.
I’m sorry . . . what campaign are you witnessing? Which email scandal are you following?
Right now, there’s no smoking gun email showing a quid pro quo. So Hillary has been given a pass by her operatives in the media, which is a nearly overlapping Venn diagram. There’s no classified document that Clinton’s operatives in the U.S. government (another near-overlapped Venn diagram) will release.
ALL THOSE DAMNING DOCUMENTS ARE ON PUTIN’S SERVER. What, you think the Russians are good enough to get the DNC’s emails but not Clinton’s nearly unprotected “private” server?
Those emails get dumped via Wikileaks and it’s a whole new ballgame. Impeachment-schmeeshment. Hillary will be politically destroyed and doubly-disgraced: the crimes plus the fact Putin had her by the (you get the idea) the whole time.
What’s she going to say? “Actually, it wasn’t the Russians feeding Wikileaks after all.” Right. She’s going to be the world’s biggest laughingstock, unable to get anything done internationally or domestically.
Which is why Putin has no interest in destroying her. Fortunately for him, she has even less reason to risk being revealed.
True. They’re exquisitely successful at besting the GOP- but I suspect their competence is roughly along the lines of the democrats of the Antebellum South, who quite successfully destroyed the Whigs, earning them a much more effective enemy.
And I have too. By now, I suspect their incompetence is a show, because I don’t really see much evidence that they even want to defeat the left.
They want to put up a good spectacle, then go fund raise off their failure, then resume the contest with their friends across the aisle, while they decide together what to do.
On the whole, their combined incompetence is such that they’re bringing the nation to ruin, which seems to be something they haven’t even noticed, or thought possible.
Hence, Trump.
I’ve said it probably too often to anyone within earshot . . . for all intents and purposes, there’s one party in Washington, DC — the Incumbency Party. They are united in defense of the status quo, regardless of what words leave their lips. Trump threatens GOP lifers far more than Hillary. Cruz similarly committed the unpardonable sin of calling out the phonies and—what’s worse—having the intellectual chops to actually do something effective about it.